Create Azure App Registration¶
Synchronizing data from Microsoft Defender for Endpoint is done using application permissions. Here we are configuring the permissions required for Power BI to connect to the Microsoft API's to retrieve the data.
Prerequisites: The user performing this step requires Global Admin and Subscription Admin rights.
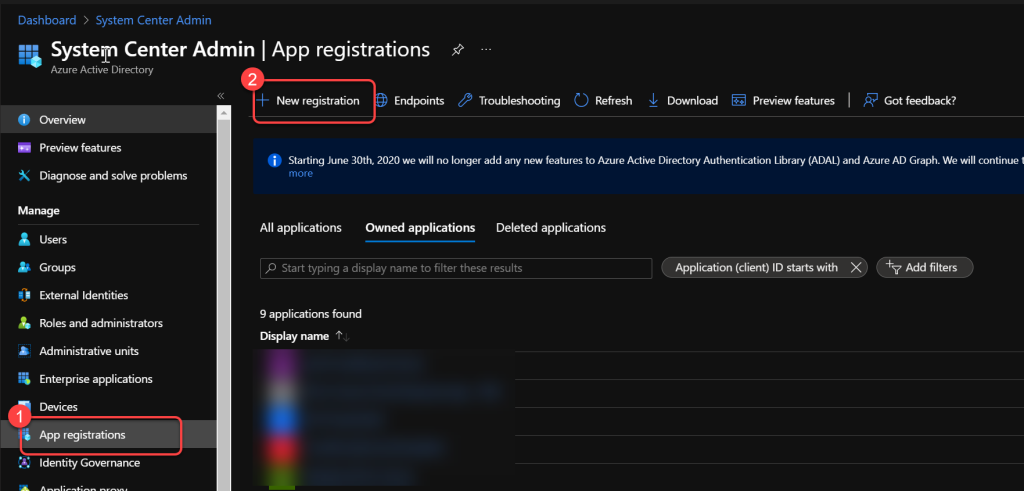
Step 1: Create a New App Registration¶
- Log in to portal.azure.com using a global administrator account.
- Search for and select App registrations.
- Select New registration.
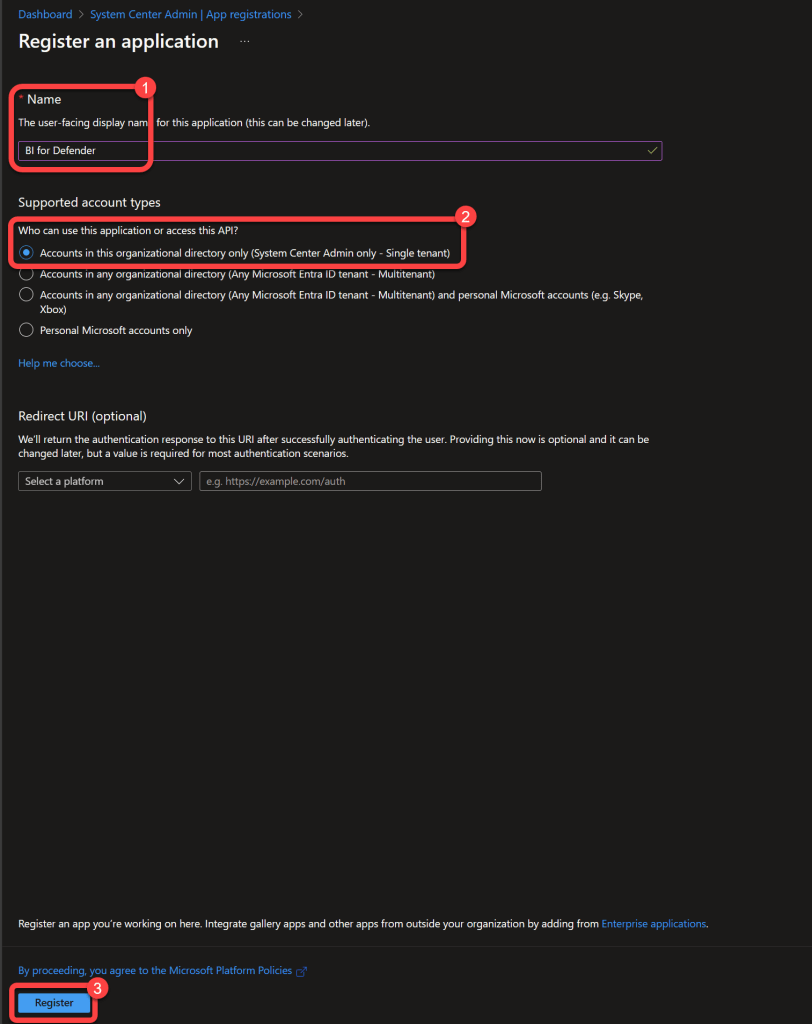
Step 2: Register the Application¶
- Enter a Name for the application. (This will not be seen by anyone other than admins.)
- Specify who can use the application as Accounts in this organizational directory only.
- Select Register.
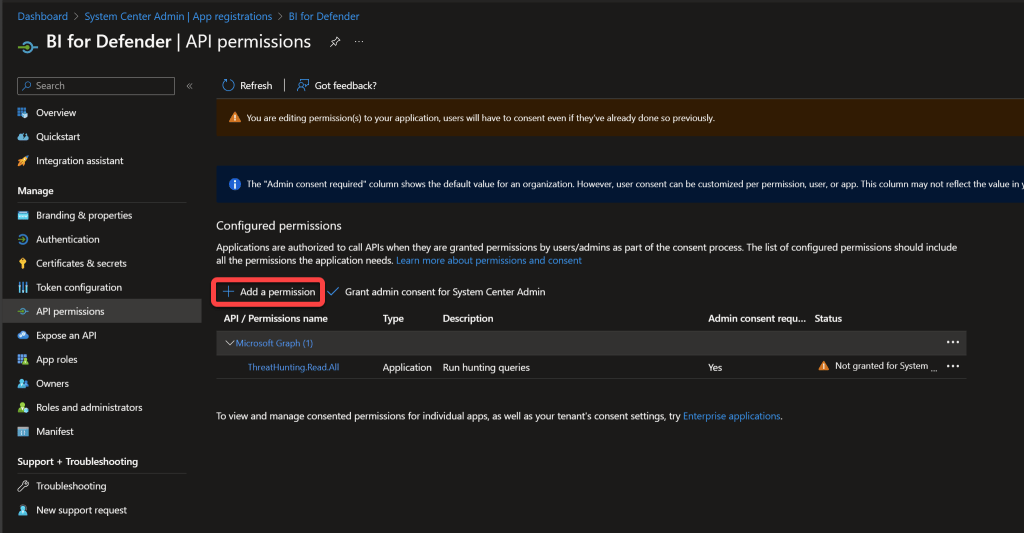
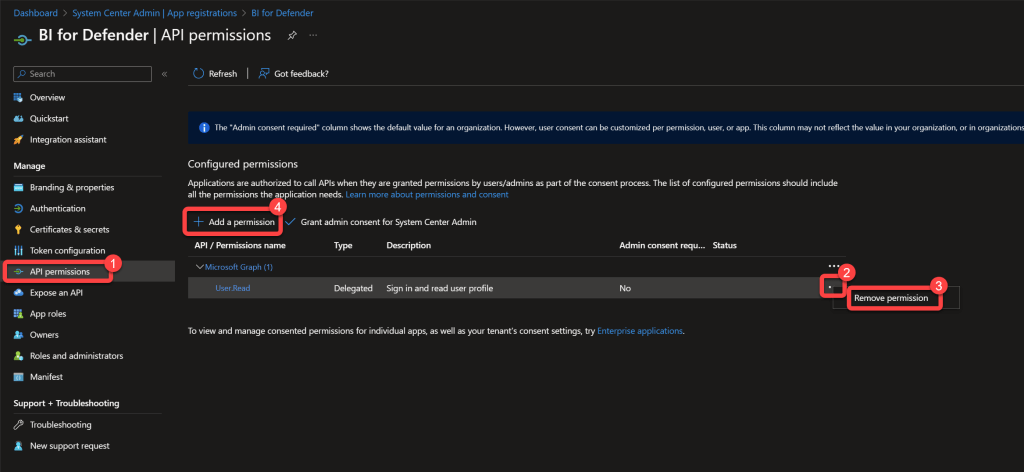
Step 3: Open API Permissions¶
- On the Enterprise App page select API Permissions.
- Remove the User.Read permission.
- Select Add a permission.
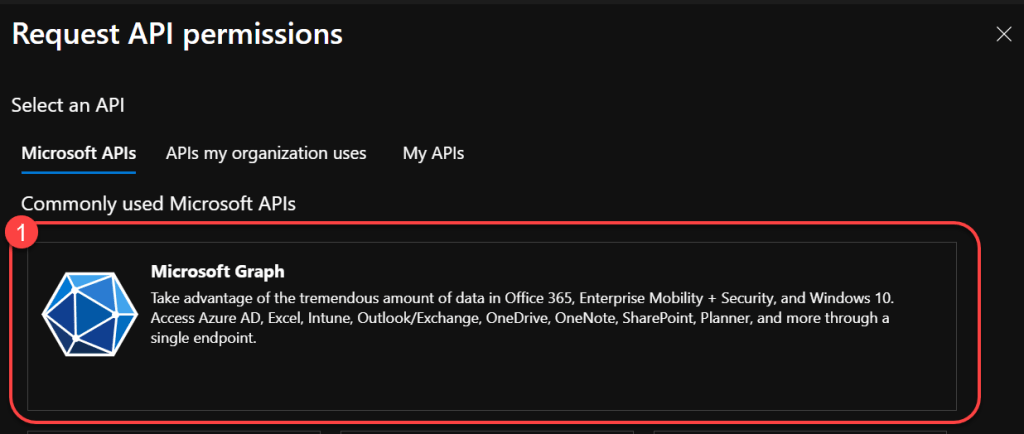
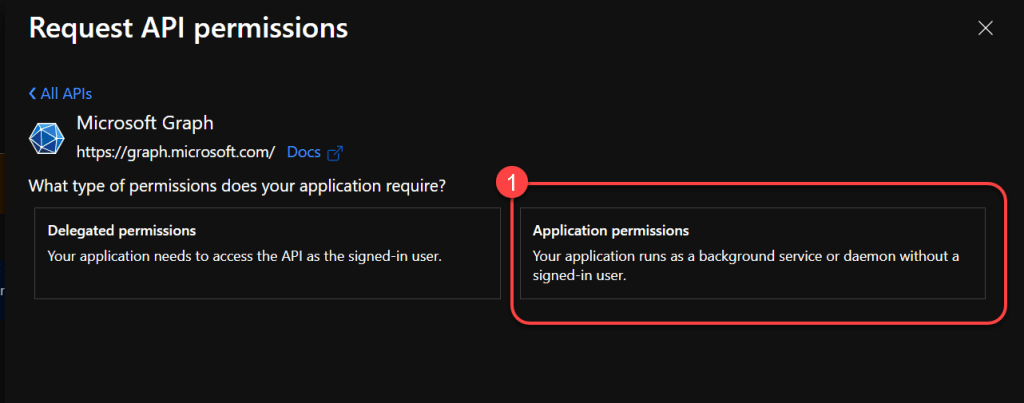
Step 4: Select Microsoft Graph¶
Step 5: Choose Application Permissions¶
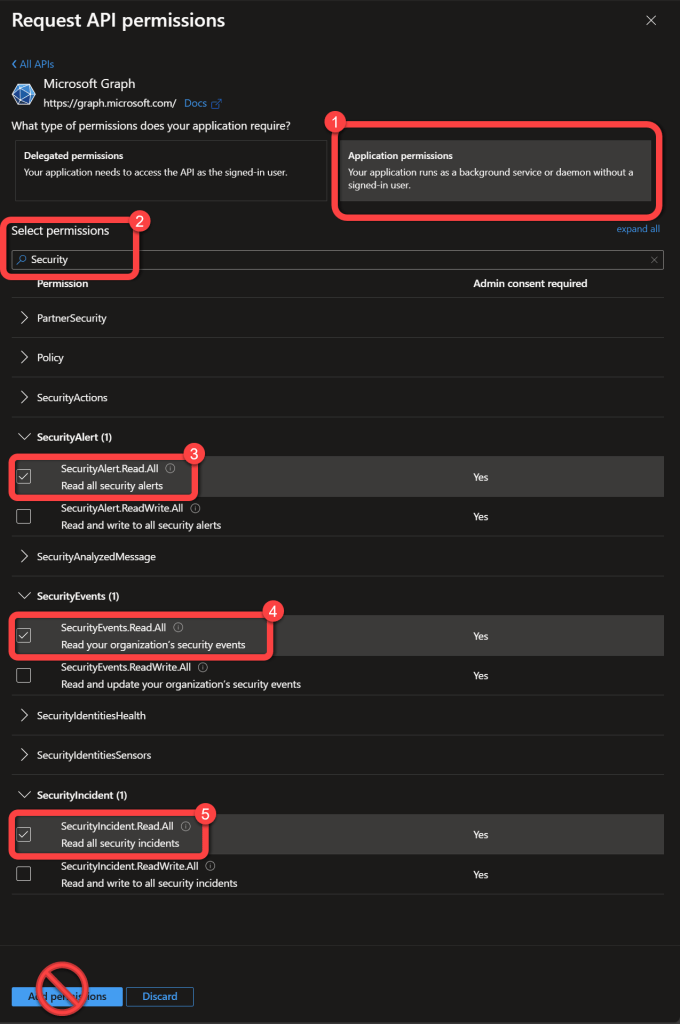
Step 6: Add Security Permissions¶
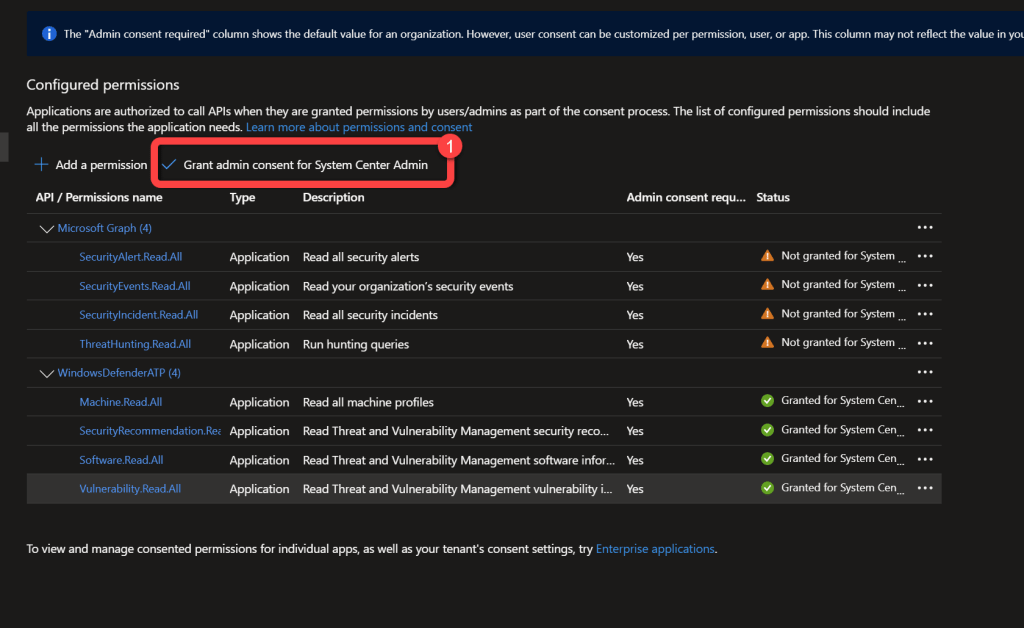
- Search for Security.
- Select the following permissions:
- SecurityAlert.Read.All
- SecurityEvents.Read.All
- SecurityIncident.Read.All
- Do not select the Add permissions button, continue to the next step.
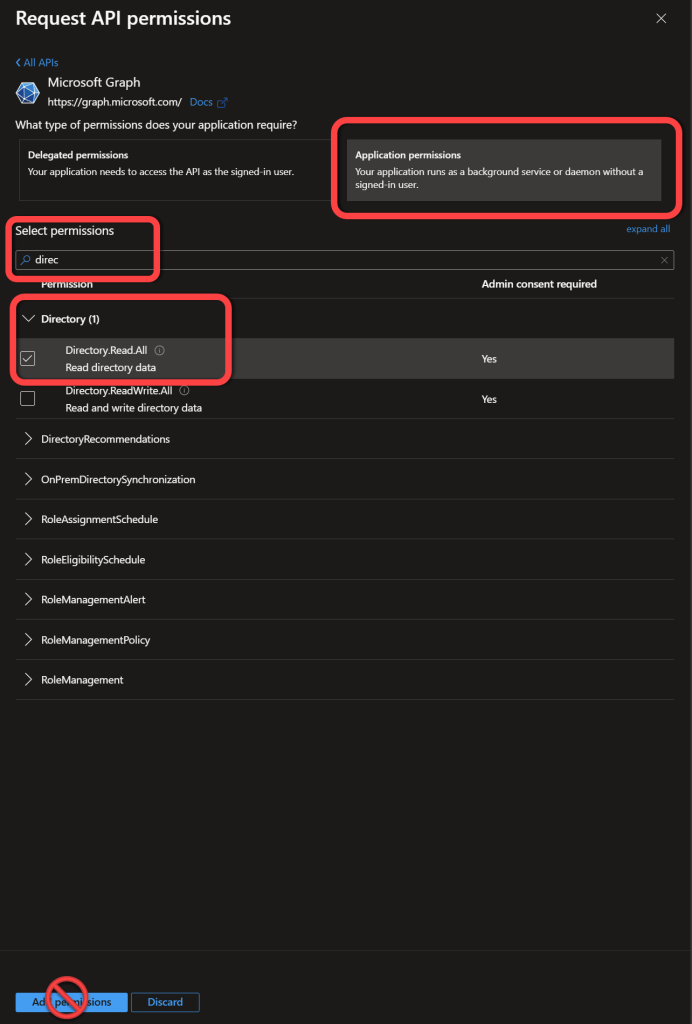
Step 7: Add Directory Permissions¶
- Search for Directory.
- Select the following permissions:
- Directory.Read.All
- Do not select the Add permissions button, continue to the next step.
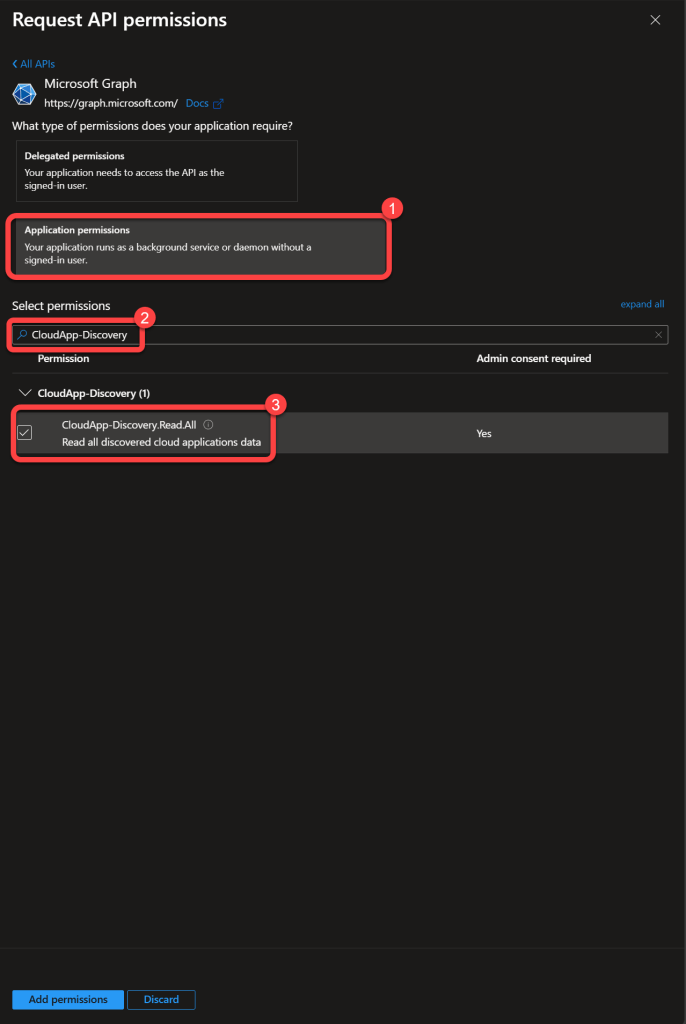
Step 8: Add CloudApp-Discovery Permissions¶
- Search for CloudApp-Discovery.
- Select the following permissions:
- CloudApp-Discovery.Read.All
- Do not select the Add permissions button, continue to the next step.
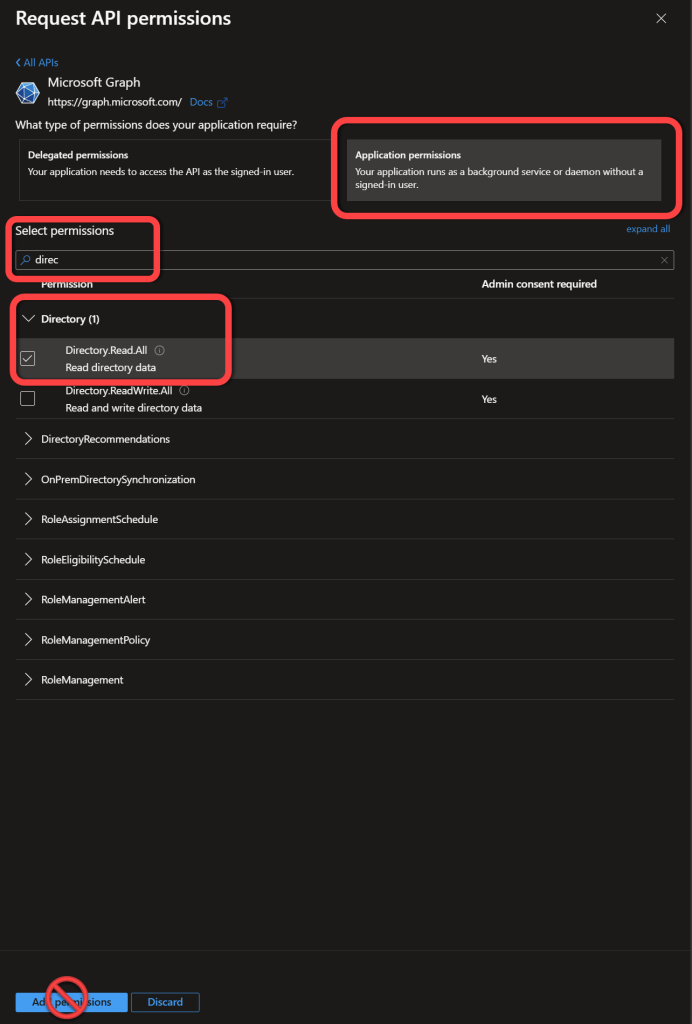
Step 9: Add Additional Directory Permissions¶
- Search for Directory.
- Select the following permissions:
- Directory.Read.All
- Do not select the Add permissions button, continue to the next step.
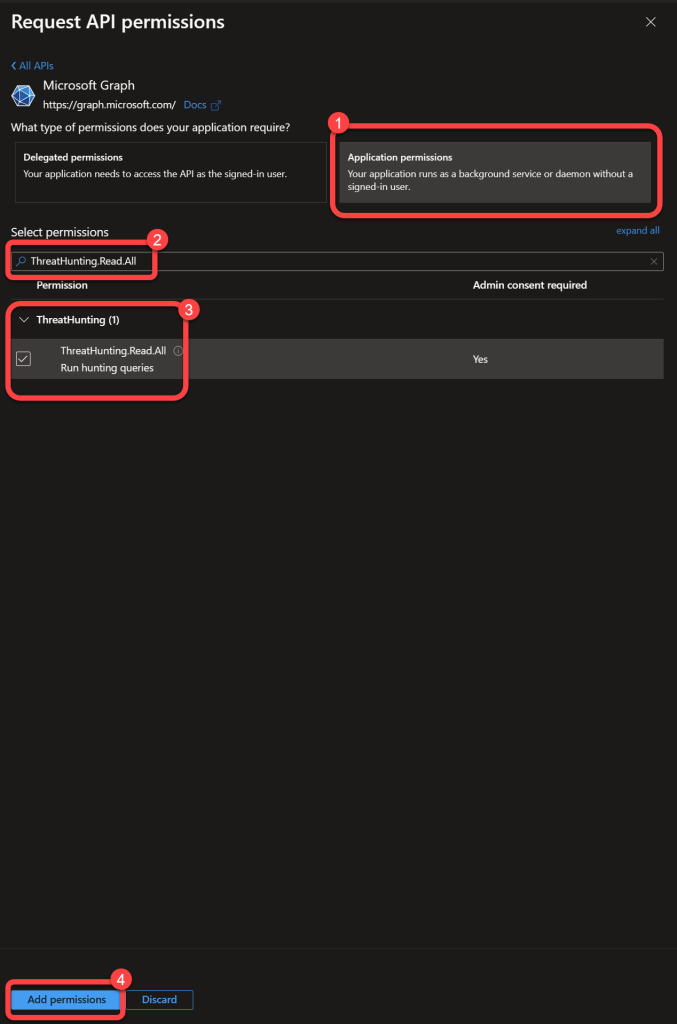
Step 10: Add ThreatHunting Permissions¶
Step 11: Add Another Permission Set¶
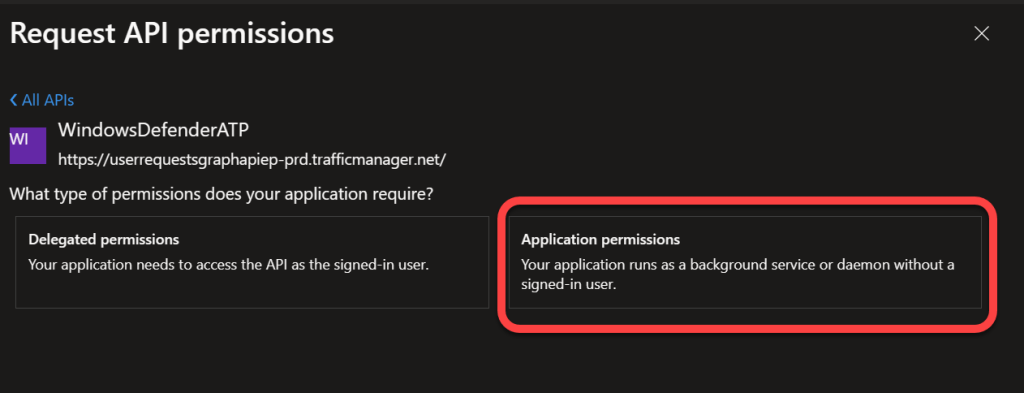
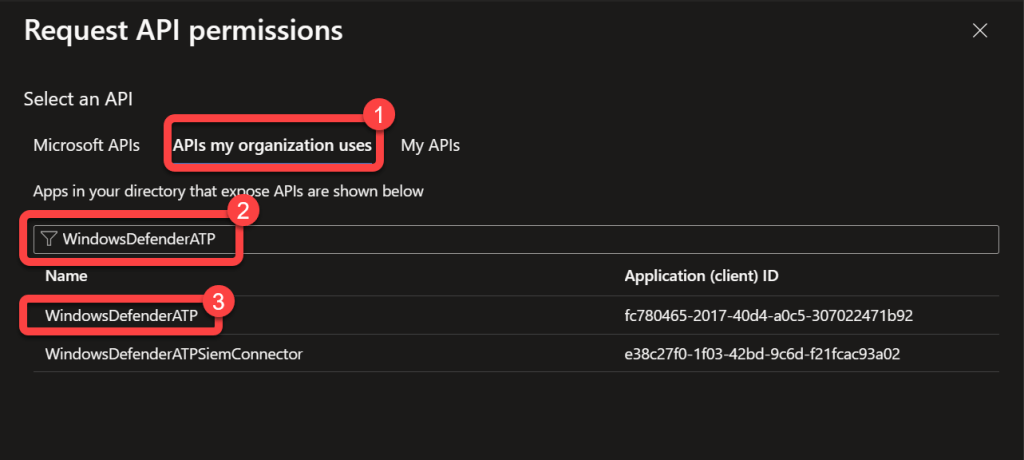
Step 12: Select WindowsDefenderATP API¶
- Select APIs my organization uses.
- Search for WindowsDefenderATP.
- Select WindowsDefenderATP in the search results.
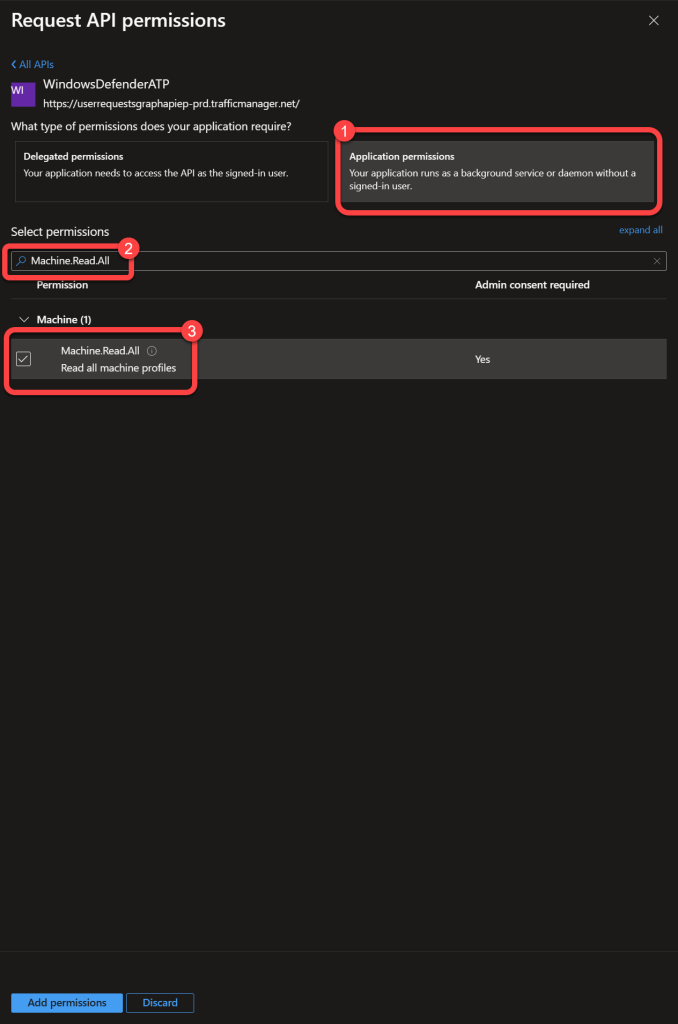
Step 13: Choose Application Permissions¶
Step 14: Add Machine Permissions¶
- Search for Machine.
- Select the following permissions:
- Machine.Read.All
- Do not select the Add permissions button, continue to the next step.
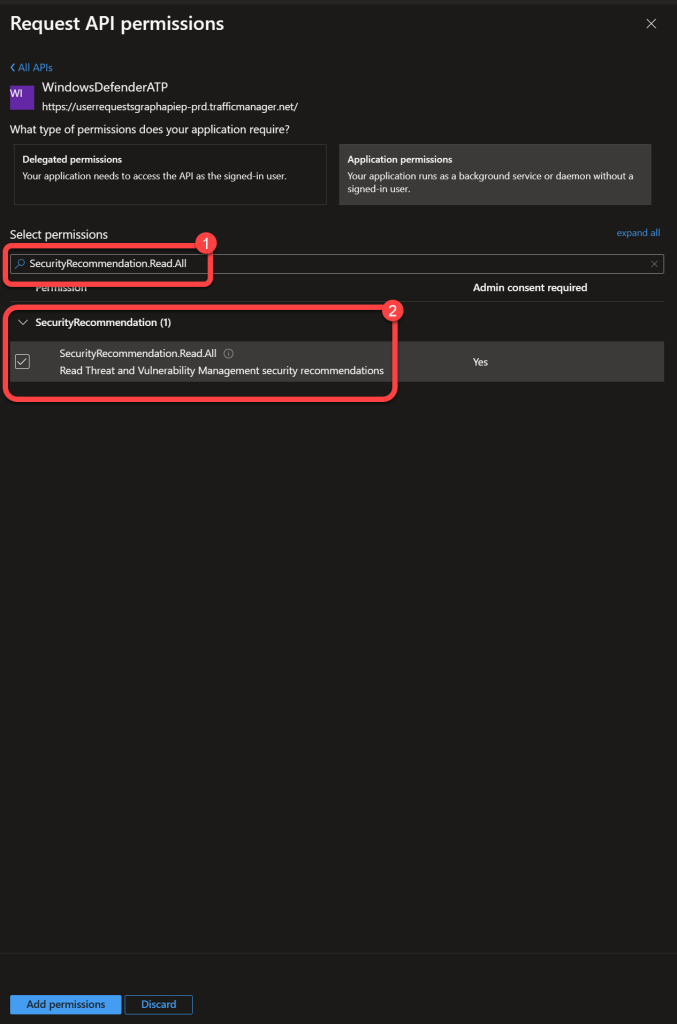
Step 15: Add SecurityRecommendation Permissions¶
- Search for SecurityRecommendation.
- Select the following permissions:
- SecurityRecommendation.Read.All
- Do not select the Add permissions button, continue to the next step.
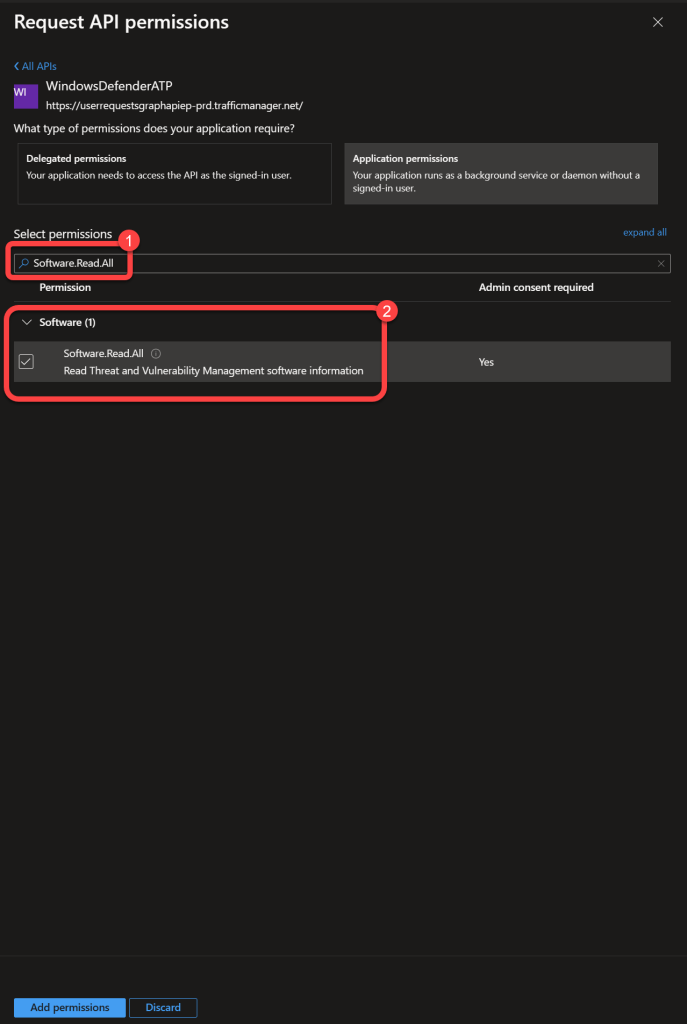
Step 16: Add Software Permissions¶
- Search for Software.
- Select the following permissions:
- Software.Read.All
- Do not select the Add permissions button, continue to the next step.
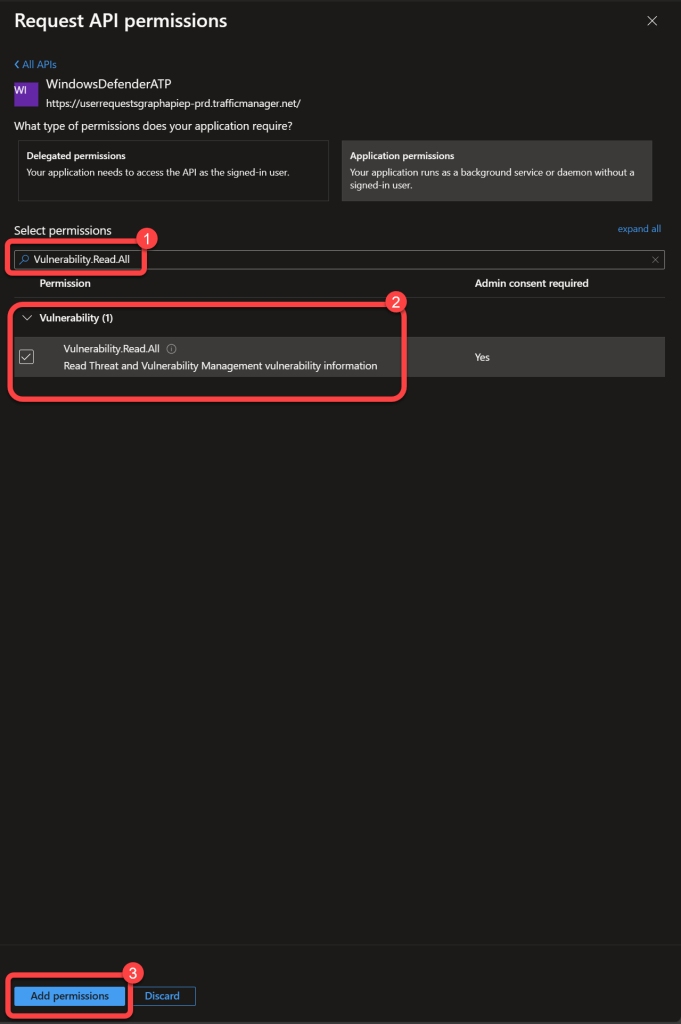
Step 17: Add Vulnerability Permissions¶
- Search for Vulnerability.
- Select the following permissions:
- Vulnerability.Read.All
- Select the Add permissions button.
Step 18: Grant Admin Consent¶
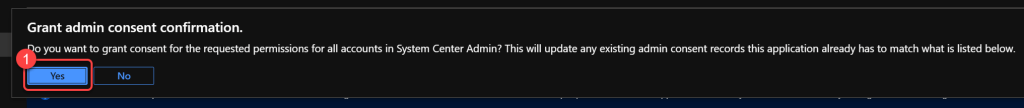
Step 19: Confirm Admin Consent¶
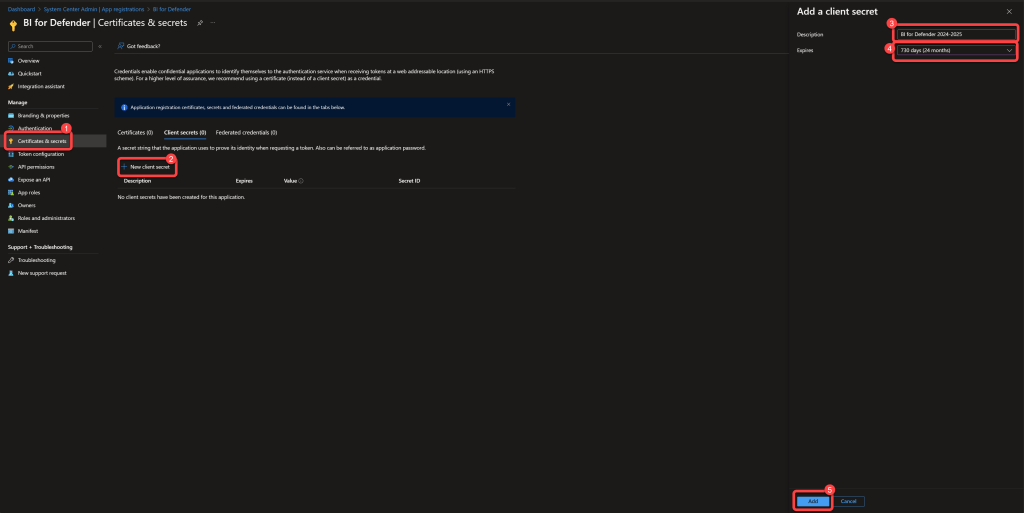
Step 20: Create a Client Secret¶
- Select Certificates & secrets.
- Select New client secret.
- Enter a Description.
- Select a value for Expires.
- Select Add.
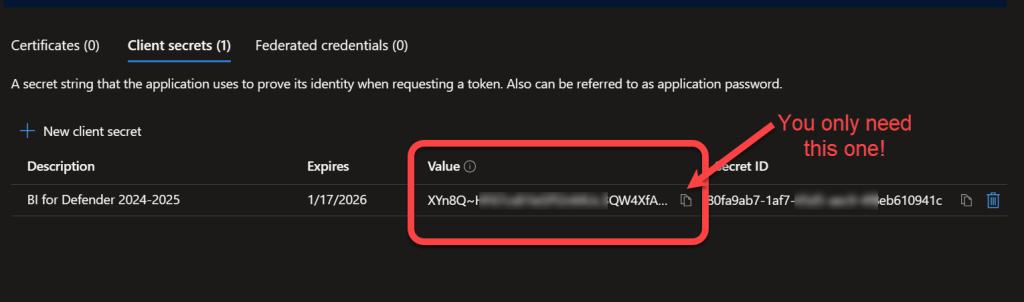
Step 21: Record the Client Secret Value¶
-
Record the Value data as the Azure AD Client Secret. This will be used later in the installation process. The value can only be displayed once, if you fail to record it here you will have to create a new one.
Warning
This is the most common mistake made. You do not need the Secret ID. You just need the Value.
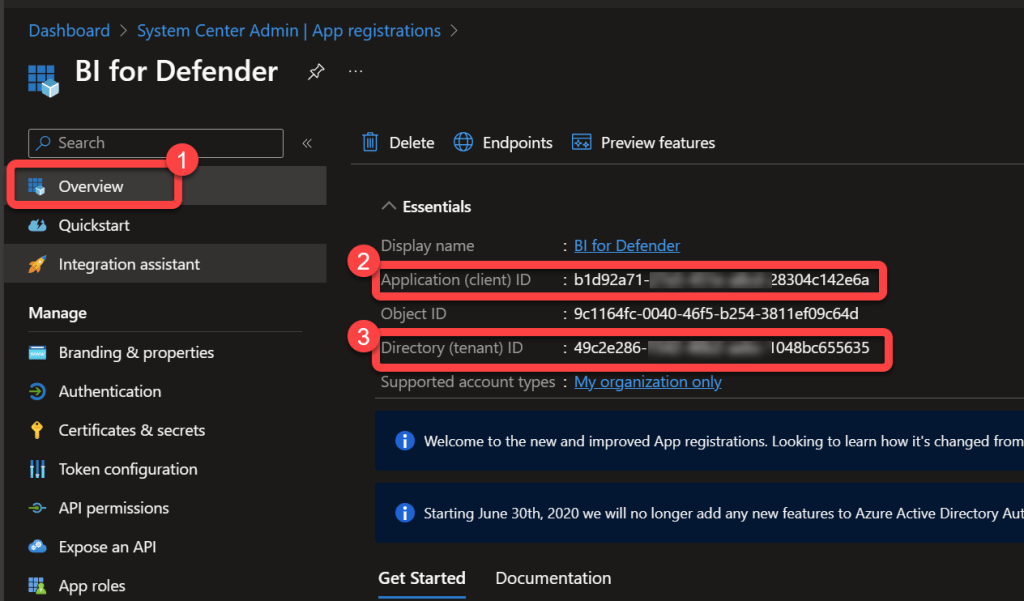
Step 22: Record the App and Tenant IDs¶
-
Select Overview.
- Record the Application (client) ID as the Azure AD Client ID. This will be used later in the installation process.
- Record the Directory (tenant) ID as the Azure AD Tenant ID. This will be used later in the installation process.
- The Azure AD Application registration is now complete.